Self-Hosted Infrastructure Stack: 5-Machine Tailscale Mesh
Self-Hosted Infrastructure Stack
The Architecture
Five machines connected via Tailscale mesh network, forming a private overlay network with zero public inbound ports. The machines span cloud providers (Oracle Cloud free tier, DigitalOcean) and architectures (ARM64, x86), unified under a single management plane.
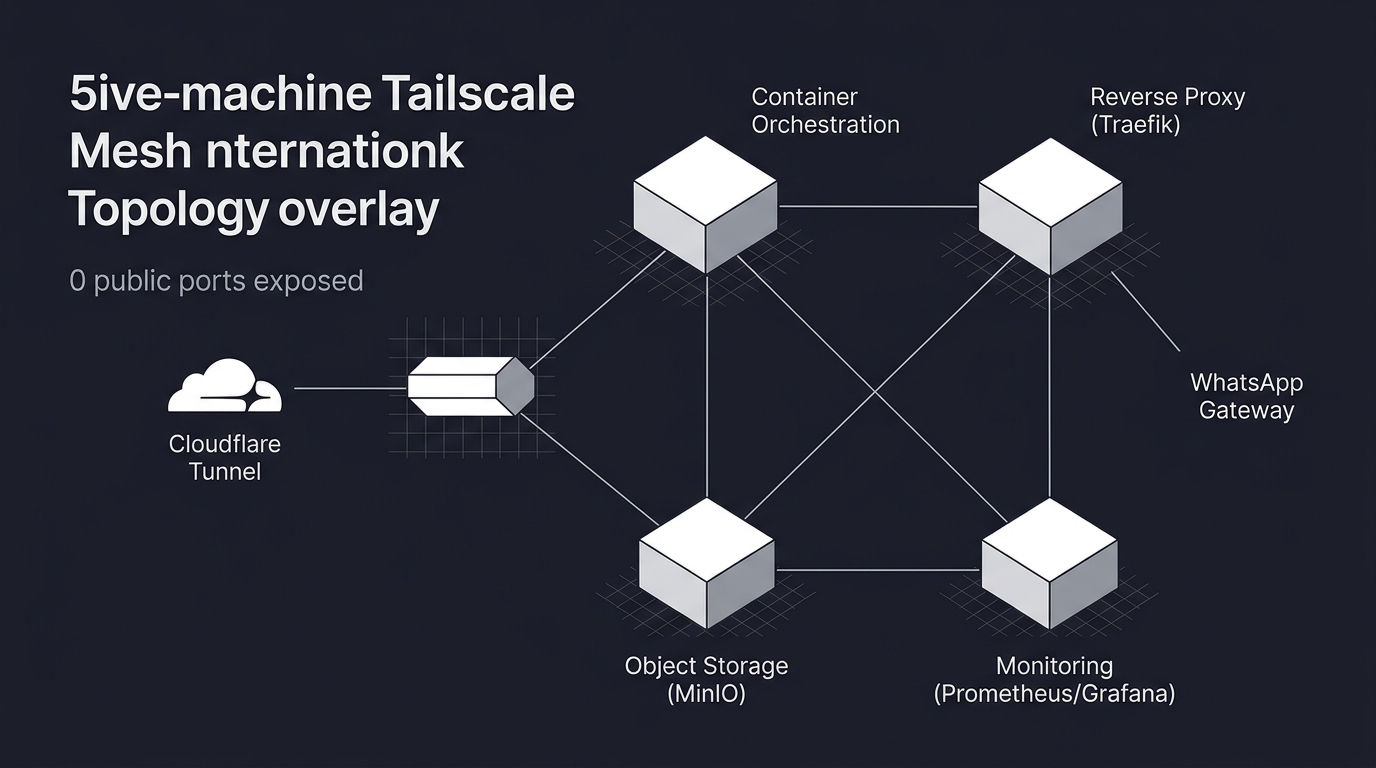
Container Orchestration. The deployment platform handles container orchestration and deployment. It is a self-hosted alternative to managed PaaS providers, providing a deployment dashboard for Docker containers without per-container pricing. All client applications, internal tools, and automation infrastructure deploy through this platform.
Traefik serves as the reverse proxy and automatic SSL termination layer. Every service gets HTTPS automatically via Let's Encrypt, with routing rules defined in Docker labels rather than nginx configuration files. Cloudflare Tunnel sits in front of Traefik for public-facing services, meaning the actual server IP is never exposed.
MinIO provides S3-compatible object storage, self-hosted. Used for newsletter image assets (CDN-proxied for public reads), backup storage, and application file storage. The decision to self-host object storage rather than use S3 directly was driven by cost (free tier) and data sovereignty (Malaysian client data stays on infrastructure I control).
WhatsApp API Gateway. A self-hosted WhatsApp Business API gateway providing HTTP endpoints for sending and receiving WhatsApp messages without relying on third-party SaaS middleware. It enables the WhatsApp automation workflows described in the automation practice.
Monitoring runs Prometheus for metrics collection and Grafana for dashboards. Uptime monitoring, container health, disk usage, and network metrics are tracked across all five machines.
Security Incident: CVE-2025-66478
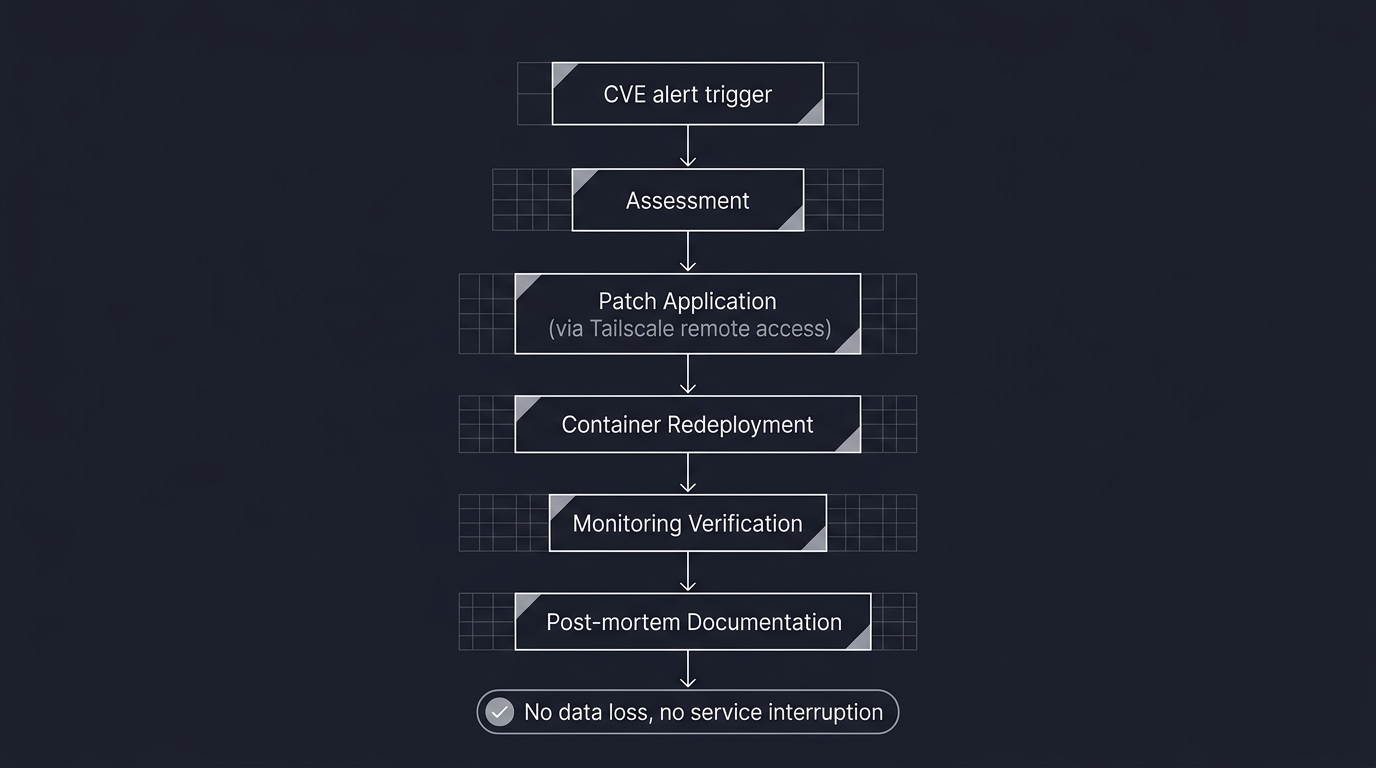
The architecture was validated under real conditions when CVE-2025-66478 required an emergency response. The vulnerability affected a component in the stack and required rapid assessment, patching, and verification across all machines.
The response demonstrated that the infrastructure was designed for exactly this scenario: Tailscale mesh meant patches could be applied remotely without exposing management interfaces. The deployment platform's container-based architecture meant affected services could be redeployed with patched images without downtime to unaffected services. The monitoring stack provided immediate visibility into whether the vulnerability had been exploited before patching.
The incident was contained with no data loss, no service interruption, and no client impact. The post-mortem documented the response timeline and identified improvements to the patching workflow.
What This Demonstrates
Production infrastructure operation, not just deployment scripting. A coherent architecture where every component (mesh networking, container orchestration, reverse proxy, object storage, monitoring) serves a specific purpose and the interactions between them are understood. Cost discipline: this entire stack runs on free tier and minimal-cost instances, proving that enterprise-grade infrastructure patterns do not require enterprise budgets. Security-first design (zero public ports, Tailscale mesh, Cloudflare Tunnel) validated by a real incident response. And the operational maturity to maintain, monitor, and defend running infrastructure, not just build it.
See also: Workflow Automation Practice and Ephemeral Deployment Architecture.
* Images are conceptualized, not the real implementation to protect client's intellectual right